Why Technology Secrecy Is Short-Lived—and Operational Mastery Is Decisive
Strategic Takeaway:
Secrecy in warfare has not disappeared—but it has shifted. What has collapsed is the lifespan of technology secrecy, not operational secrecy. Advantage now lies in how fast a military can convert visible technology into force-wide capability.
Executive Summary
Military organizations today face a persistent dilemma: protect emerging capabilities within specialized units or rapidly disseminate them across the force.
For decades, secrecy provided a clear answer. Capabilities could be developed quietly, refined internally, and revealed only when operationally decisive.
That model assumed time.
Modern warfare no longer guarantees it.
Across conflicts—from the Russo-Ukrainian War to the ongoing confrontation involving Iran, Israel, and the United States—a pattern emerges:
The existence of a capability becomes visible quickly. What remains decisive is how it is employed.
Advantage no longer comes from possessing a capability first, but from scaling its effective use faster than others can adapt.
The Distinction That Matters: Technology vs. Operational Secrecy
Secrecy in warfare is not a single concept.
Technology secrecy refers to hiding the existence or general function of a system. Operational secrecy refers to concealing how that system is used—targeting, timing, sequencing, and integration.
This distinction is analytically important in modern contexts.
Technology is increasingly observable and replicable. Operations remain contextual, intelligence-driven, and difficult to copy.
You can hide intent longer than you can hide tools.
Israel: The Real Lesson on Secrecy
Israel is often cited as proof that secrecy still defines modern warfare.
It does—but not in the way commonly assumed.
Israel tightly protects intelligence sources, targeting decisions, and the timing and sequencing of operations. But the technologies themselves—drones, precision munitions, ISR systems—are widely known and increasingly emulated.1
Israel’s advantage is not technological exclusivity.
It is operational mastery under conditions where technology is already visible.

Why Technology Secrecy Has a Short Lifespan
This shift is driven in part by accessibility. Modern capabilities are often built on commercially available systems—drones, AI tools, sensors, and communications platforms—accessible to a wide range of actors. What was once exclusive to advanced militaries is now more broadly procurable and adaptable.
At the same time, the battlefield has become increasingly transparent. Operations are recorded, shared, and analyzed in near real time. Even without official disclosure, capabilities are observed and examined through open sources. A single engagement, a published exercise, or a leaked video can expose TTPs to global audiences within hours.1
Overlaying both is the impact of artificial intelligence, which compresses the analysis-to-action cycle. In previous eras, observing a capability was only the first step—understanding it, replicating it, and deploying a counter still required time and institutional capacity. AI appears to remove much of that friction in many contexts. Adversaries can process large volumes of open-source imagery, signals data, and battlefield footage to identify patterns, infer TTPs, and generate countermeasures faster than traditional intelligence workflows allowed.2
The result is a rapid loop:
Observe → Adapt → Counter
In many cases, this loop now moves faster than institutional adaptation cycles.
The AI Factor: From Observation to Exploitation
Of the forces compressing the lifespan of technology secrecy, artificial intelligence warrants separate attention—not simply as an accelerator, but as an enabler of new forms of analysis from observation alone.
Traditional intelligence processes required significant resources to convert raw data into actionable understanding. Satellite imagery was reviewed by trained analysts, signals were processed through specialized pipelines, and battlefield footage was manually examined. These steps introduced natural lag—time that allowed militaries to manage the consequences of exposure.
AI reduces that lag.
Modern systems can process open-source imagery at scale, identifying equipment, positions, and movement patterns faster than human teams. They can analyze footage from multiple engagements simultaneously to infer tactical patterns and generate countermeasure options without waiting for formal doctrine cycles.2
The implication is direct:
A capability observed once can be analyzed, understood, and countered faster than the force that deployed it can adapt its own TTPs.
This creates a new asymmetry—not between those who possess technology and those who do not, but between institutions that can absorb and act on AI-enabled intelligence and those that cannot.
For militaries such as the AFP, this cuts both ways.
Concealment of capabilities in contested environments becomes more fragile, as AI-enabled systems can extract patterns from repeated operations, patrol routes, and response behaviors at scale. At the same time, accessible AI tools—commercial imagery analysis, open-source pattern recognition, AI-assisted targeting—offer opportunities to offset resource constraints if institutionalized quickly enough.
AI has shortened the lifespan of secrecy and elevated organizational speed as the primary hedge against exposure.
Ukraine: Scaling Faster Than the Enemy
The war in Ukraine illustrates how rapid adaptation can shape operational advantage.
Drone technology itself was not unique. What proved significant was the speed with which it was integrated into operations.2,3 Tactical units incorporated drones directly into targeting cycles, enabling near real-time adjustment of fires and reconnaissance at the unit level. Field-level adaptations were shared across formations, allowing practices developed in one sector to propagate quickly to others.
Within a relatively short period, drones shifted from niche capability to standard tool across multiple echelons.
Ukraine also reflects the AI dimension. Both sides appear to have incorporated increasingly automated and AI-assisted approaches to targeting, drone employment, and electronic warfare countermeasures. The advantage at any given moment tended to align with the force that absorbed these tools into institutional workflows more quickly—not the one that first fielded them.3
The advantage was not invention. It was diffusion.
The Middle East: Visible Technology, Hidden Logic
The ongoing confrontation involving Iran, Israel, and the United States highlights a different dimension of the same dynamic.
Drones, missiles, and maritime attack systems are visible, publicly reported, and rapidly analyzed. Their existence is not secret.1
Yet outcomes remain difficult to predict.
This is not due to lack of information about the technology, but because execution remains opaque—targeting logic, sequencing, system integration, and the intelligence informing decisions are not directly observable.
Technology is visible. Execution is not.
Marawi (2017): The Cost of Learning in Contact
The Battle of Marawi provides a critical Philippine lesson.
In 2017, the Armed Forces of the Philippines confronted a large-scale urban battle it had not recently trained for at scale. Relevant skills existed within parts of the force, but they were not sufficiently institutionalized and diffused across conventional units before the fight.4
During early operations, units entering dense urban terrain adjusted clearing techniques in contact, often learning from adjacent units or recent engagements rather than from standardized, pre-distributed training. What proved effective in one sector was shared informally, but took time before those adaptations became consistent across units.5,6
Units adapted in contact. Coordination improved during operations. Tactical solutions emerged bottom-up before being formalized.
The issue was not absence of capability.
It was the gap between existing knowledge and force-wide readiness.
This remains relevant in a faster-evolving operational environment. The adaptation gap now extends beyond urban tactics to include drone integration, AI-assisted targeting, and real-time ISR—capabilities that are increasingly visible and replicable across conflicts.
The risk is not only being unprepared for terrain—but being late in adopting modes of warfare already observable globally.
Marawi’s enduring lesson: Delayed diffusion can create operational risk—particularly in environments where learning cycles are accelerating.
The Real Source of Advantage
Technology is global. Capability is institutional.
What matters is not possession, but integration into operations, translation into training, and speed of dissemination across units.
In modern operational environments, technology rarely remains exclusive for long. What differentiates forces is not access, but absorption—how quickly tools are converted into usable, repeatable practice across the force.
This shifts the basis of advantage away from possession and toward process.
Organizational speed becomes central. It shapes how quickly lessons are learned, how effectively they are shared, and how consistently they are applied across units.³
In environments where adversaries are simultaneously observing and adapting—often with the aid of AI-enabled analysis—the gap between exposure and countermeasure continues to narrow. Under these conditions, slow institutional response can erode the value of any capability, regardless of its technical sophistication.
In this context, advantage increasingly reflects how fast an institution can learn and adapt—not what it possesses.
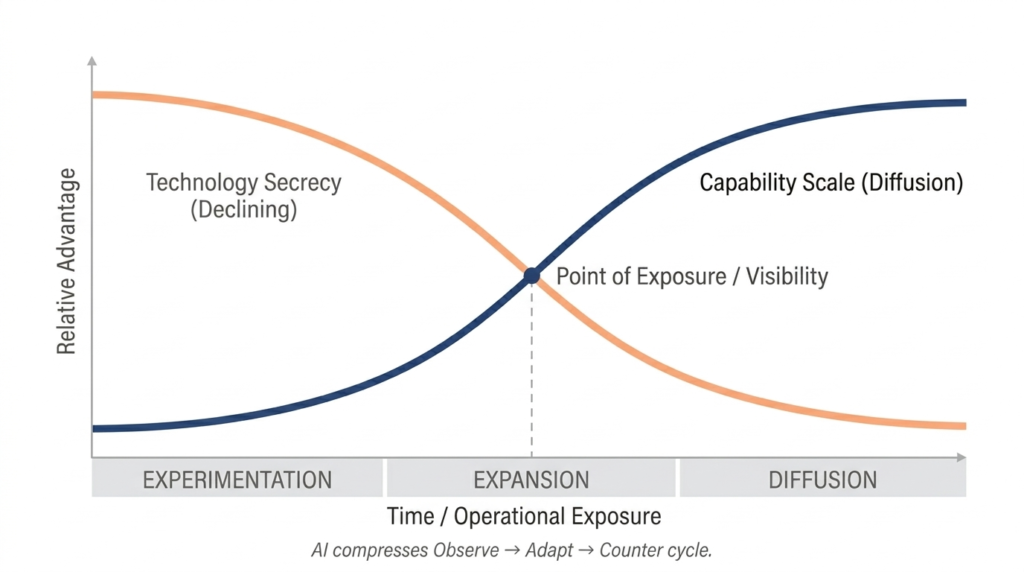
Managing the Tension: From Secrecy to Scale
The tension between secrecy and rapid adoption is real—but it is better understood as a sequence rather than a binary choice.
Phase 1 – Controlled Experimentation: Early learning is protected. Specialized units test and refine TTPs before wider exposure.
Phase 2 – Structured Expansion: Training systems and initial doctrine are developed. Selected units begin adopting the capability.
Phase 3 – Rapid Diffusion: Capability scales across the force. Variations in proficiency are accepted as learning continues.
In practice, these phases rarely unfold sequentially. In fast-moving environments, elements of rapid diffusion may occur before structured expansion is complete, particularly under pressure from adversarial adaptation.
In practice, diffusion is shaped by institutional constraints. Training pipelines are scheduled in advance, doctrine updates take time to disseminate, and unit rotations affect continuity. Instructor capacity can vary across institutions, influencing how quickly new capabilities are absorbed.
These frictions do not prevent adaptation—but they slow it.
In an environment where AI is compressing adversarial learning cycles, institutional delay becomes operationally significant faster than before.
Advantage comes from moving between phases faster than an adversary—and from embedding AI literacy across all phases, not only at the point of full-scale adoption.
Implications for the Philippines
For the Armed Forces of the Philippines, these dynamics are no longer theoretical.
Marawi demonstrated the risks associated with delayed diffusion. Current operating conditions suggest that such risks may emerge more quickly.
A recent example is the 2024 resupply missions to the BRP Sierra Madre at Ayungin (Second Thomas) Shoal. These operations occurred under constant observation and active contestation. Chinese vessels monitored movements, confrontations were recorded and circulated, and incidents involving water cannons, vessel damage, and personnel injury were reported and analyzed in near real time.78910
What is less visible but equally significant is the analytical layer behind that observation. Maritime surveillance increasingly integrates AI-enabled pattern recognition—processing vessel movements, resupply timings, and response behaviors at a scale that manual analysis could not sustain. Each operation becomes a source of data for ongoing assessment.
In such an environment, capability exposure occurs quickly. Operational patterns are studied, and responses are adjusted.
Technology and broad actions are visible. Operational intent and execution remain decisive.
Capabilities such as drone operations, ISR integration, AI-assisted analysis, and digital targeting therefore cannot remain confined to specialized units indefinitely. Their impact depends on how early and how broadly they are diffused across the force.
Training institutions play a central role in this process. Building baseline AI literacy—not advanced technical specialization, but operational understanding—enables commanders and staff to integrate these tools into planning and execution cycles.
Accessible tools—OSINT, commercial AI, open-source imagery analysis—present opportunities to offset resource constraints, but only if they are institutionalized at speed.
Conclusion
Secrecy remains a fundamental element of warfare.
But its role has shifted.
Technology secrecy is short-lived. Operational secrecy remains decisive.
Artificial intelligence has accelerated this shift significantly by compressing the time between observation and exploitation, reducing the window for controlled experimentation, and increasing the cost of institutional delay.
This changes how advantage is built—not by who possesses a capability, but by who can integrate it, institutionalize it, and scale it faster than others can respond.
In fast-changing operational environments, slow diffusion becomes a vulnerability.
Advantage will favor forces that can learn, adapt, and scale faster than their adversaries—at the level of the institution, not the individual unit.
Endnotes
1 International Institute for Strategic Studies. The Military Balance 2024. London: IISS, 2024.
2 Schmid, Jon, and Erik E. Mueller. “What the Pentagon Might Learn from Ukraine About Fielding New Tech.” RAND Corporation Commentary, February 14, 2025. Available at rand.org.
3 Center for Strategic and International Studies. Lessons from the Ukraine Conflict: Modern Warfare in the Age of Autonomy, Information, and Resilience. CSIS, May 2, 2025. Available at csis.org.
4 Franco, Joseph. “The Battle for Marawi: Urban Warfare Lessons for the AFP.” Security Reform Initiative Working Paper, October 4, 2017. Available at securityreforminitiative.org and ResearchGate.
5 Bajo, Ann. “Fighting in Cities: Insights from the Battle of Marawi.” Canadian Army Journal 21, no. 2. Available at canada.ca.
6 Lewis, James. “The Battle of Marawi: Lessons for Developing Urban Capabilities.” Australian Army Journal 15, no. 1, Autumn 2019. Australian Army Research Centre. Available at researchcentre.army.gov.au.
7 Asia Maritime Transparency Initiative, Center for Strategic and International Studies. “Tracking Tensions at Second Thomas Shoal.” January 30, 2024. Available at amti.csis.org.
8 Asia Maritime Transparency Initiative, Center for Strategic and International Studies. “Shifting Tactics at Second Thomas Shoal.” August 22, 2024. Available at amti.csis.org.
9 Associated Press. “Chinese coast guard hits Philippine boat with water cannons in disputed sea, causing injuries.” March 23, 2024. Available at apnews.com.
10 Strangio, Sebastian. “China Coast Guard Again Damages Philippine Boat Near Disputed Shoal.” The Diplomat, March 25, 2024. Available at thediplomat.com.
About BalangAI Strategic Security Institute
BalangAI Strategic Security Institute is an independent, non-partisan policy and research organization focused on peace, security, governance, and strategic issues affecting the Philippines, Southeast Asia, and the Indo-Pacific.
Contact
For inquiries, collaboration, or speaking engagements, please visit the
About BalangAI page or reach us through the website contact channels.
